Your Voice Is the Key with Voice Biometric Authentication
Think about the last time you had to reset a forgotten password. Frustrating, right? Now, imagine unlocking your most important accounts—your bank, your health records—just by speaking a simple phrase. That's the core idea behind voice biometric authentication, a technology that uses your unique voice as a digital key.
It’s a fundamentally different approach to security, one that’s both faster and far more secure than the methods we've grown used to.
Your Voice Is the Future of Authentication

For decades, we’ve leaned on passwords and PINs, but let's be honest—they’re broken. We forget them, they get guessed, or worse, they're stolen in huge data breaches, putting our entire digital lives at risk. Voice biometrics offers a compelling alternative by analyzing the one-of-a-kind characteristics of your speech.
Your voice is a lot like your fingerprint. It's made up of more than a hundred distinct physical and behavioral traits that are incredibly difficult for anyone else to replicate. These traits fall into two main categories:
- Physiological traits: Things you can't control, like the unique size and shape of your larynx, vocal tract, and even your nasal passages.
- Behavioral traits: The subtle ways you speak, including your personal rhythm, accent, cadence, and pitch.
Together, these elements create a "voiceprint"—a secure, mathematical model of your voice. When you speak to log in, the system isn't just listening to what you say; it's analyzing how you say it, comparing the live audio to your stored voiceprint to confirm it's really you.
Why Voice Is Gaining Momentum
The move toward voice-based security is more than just a passing trend. It's a direct response to the need for stronger security that doesn't get in the user's way. Traditional methods often create friction, forcing you to juggle complex passwords or recall the name of your first pet. Voice authentication cuts through that noise, making access feel natural and effortless.
Voice biometrics turns a security checkpoint into a simple conversation. Instead of typing or tapping, you just speak. That convenience is a huge part of why it's catching on so quickly.
The numbers back this up. The global voice biometrics market was valued at around USD 2.39 billion and is expected to hit USD 7.01 billion by 2032, growing at an impressive 16.6% each year. This boom is driven by real-world uses in banking, healthcare, and e-commerce for everything from fraud detection to securing confidential records. You can dig deeper into the voice biometrics market growth to see just how fast it's expanding.
In this guide, we'll cover everything you need to know about voice biometric authentication. We'll look at the AI that makes it all possible, explore how it protects your data, and walk through how to bring this technology into your own systems. You'll soon see why your voice is becoming one of the most powerful tools for digital security.
How AI Learns the Unique Sound of Your Voice
Your voice is so much more than the words you speak. It's a complex tapestry woven from hundreds of unique physical and behavioral traits. Just like a fingerprint has its own distinct ridges and whorls, your voice possesses subtle characteristics that, when combined, create a pattern that belongs only to you. This is the magic behind voice biometric authentication. The AI doesn't just hear you—it analyzes you.
Think of it like a master sommelier who can identify a specific vintage of wine just by its taste and aroma. The AI acts as a digital connoisseur for your voice, listening for the unique qualities of your vocal "instrument." It captures everything from the physical shape of your vocal tract, which dictates your pitch and resonance, to your personal speaking rhythm, accent, and cadence. These elements are then converted into a secure, digital signature.
This process creates something we call a voiceprint. It's crucial to understand this isn't an audio recording of you talking. Instead, it’s a mathematical model—a string of numbers—representing your voice's unique properties. This distinction is vital for privacy; a voiceprint can't be reverse-engineered to recreate your actual voice, making it useless to a thief.
The Two Core Approaches to Voice Verification
When it comes to verifying your identity, AI systems typically take one of two paths. The method used often comes down to the security needs of the application and the kind of user experience they want to create.
- Text-Dependent Verification: This is the more structured approach. It asks you to speak a specific passphrase, like "My voice is my password." Since the system knows exactly what you're supposed to say, it can focus entirely on how you say it. This provides a clean, consistent sample for comparison every time.
- Text-Independent Verification: This one is far more flexible and feels more natural. The system can identify you from normal, conversational speech without you needing to say a specific phrase. It's perfect for scenarios like a call center, where the AI can authenticate you in the background while you're busy explaining your problem to an agent.
Both methods are built on the same foundation—matching your live speech against your stored voiceprint—but they offer different trade-offs between convenience and control. To get a better sense of how these intelligent systems are built to recognize and respond to individual voices, it’s worth reading up on AI Voice Agents.
From Soundwave to Secure Authentication
The journey from your spoken words to a securely verified identity happens in a few key steps. First, during enrollment, the system captures a sample of your voice. This is where your unique voiceprint is created for the first time and stored away safely.
This image breaks down the three core stages of turning your voice into a secure key.
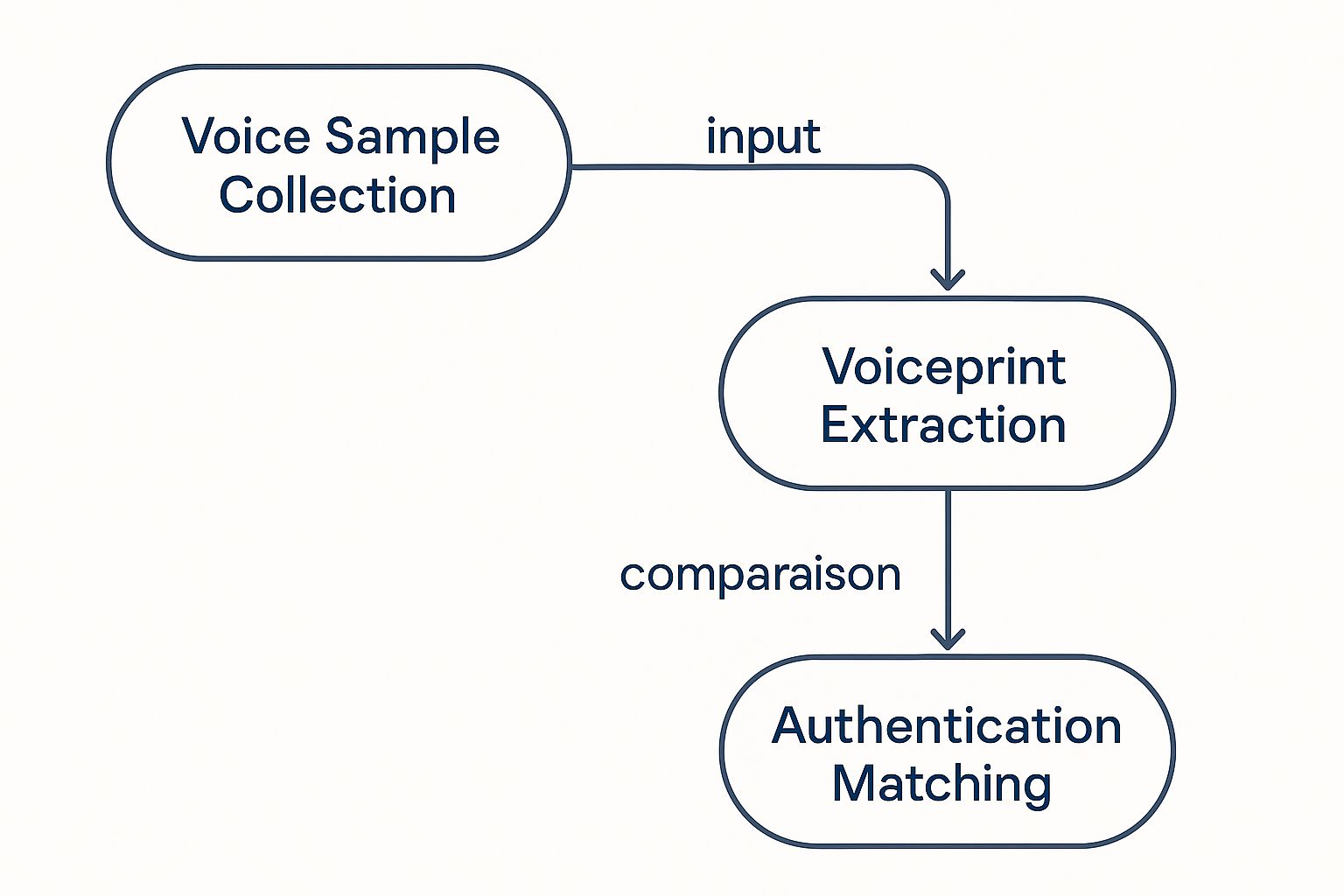
As you can see, authentication is a clear, sequential process. It starts with data collection and ends with a definitive match or rejection.
Later, when you try to log in, the system kicks off a verification process. It records your live voice and immediately performs two critical actions at once.
- Feature Extraction: The AI isolates and analyzes over 100 different vocal characteristics. These include physiological traits (like the frequency and tone produced by your vocal cords) and behavioral ones (like your speed of speech and pronunciation).
- Pattern Matching: It then compares this freshly extracted "feature set" against the mathematical model of your voiceprint in its database. The system calculates a similarity score to determine if the two patterns match with a high degree of confidence.
Here's the bottom line: The AI isn't fooled by a simple impersonation. Someone might be able to mimic your words and accent, but they can't replicate the unique physical structure of your vocal tract that produces the sound itself.
This sophisticated analysis is what makes voice biometric authentication so powerful. It goes beyond things that can be easily stolen or copied—like a password or even a signature—and verifies something that is fundamentally you. If the patterns align, you're in. If they don't, the system denies entry, stopping an unauthorized user dead in their tracks.
Strengthening Your Defenses with Voice Biometrics

In the never-ending fight against cybercrime, it's become clear that passwords and PINs are the weak links in our security chains. They're constantly targeted by fraudsters using phishing, credential stuffing, and full-blown account takeovers. This is precisely where voice biometric authentication changes the game, shifting security from something you know to something you are.
Instead of relying on a secret that can be stolen or guessed, voice biometrics verifies you based on your one-of-a-kind vocal patterns. Think about it: even if a criminal buys your login details off the dark web, they're stopped dead in their tracks when asked to speak. They simply can’t fake the more than 100 unique physical and behavioral characteristics that make up your voice.
This adds a biological lock to your digital door—one that can’t be picked with stolen keys.
The Critical Role of Liveness Detection
Cybercriminals are clever, and their latest trick is the deepfake. An audio deepfake uses AI to generate a synthetic clone of someone's voice, which could trick a less sophisticated voice system. That’s why any modern voice biometric authentication platform worth its salt includes a critical feature: liveness detection.
Think of it as the system’s way of checking, "Is this a real person speaking to me right now?" It listens for the subtle acoustic details and micro-variations in human speech that just aren't present in a recording or a synthesized voice.
This technology is designed to spot the digital fingerprints of a forgery or playback, ensuring the voice it’s hearing is coming from a living, breathing person in real-time. Without this check, any voice system would be exposed. Liveness detection is what makes voice biometrics truly resilient against today's most advanced spoofing attacks.
A voiceprint confirms who is speaking, but liveness detection confirms they are speaking live. You absolutely need both for a secure system.
Comparing Voice Biometrics to Traditional Authentication
So, how does speaking to log in stack up against the methods we're all used to? While passwords have been the standard for decades, they come with significant baggage. Let's break down the differences.
| Authentication Method | Security Level | User Convenience | Vulnerability to Theft |
|---|---|---|---|
| Voice Biometrics | Very High | High (Just speak) | Very Low (Cannot be stolen) |
| Passwords/PINs | Low | Medium (Requires memorization) | High (Phishing, data breaches) |
| SMS One-Time Codes | Medium | Low (Requires a separate device) | Medium (SIM swapping) |
| Authenticator Apps | High | Low (Requires a separate device) | Low (Requires physical device) |
As you can see, voice biometrics offers a unique blend of top-tier security without adding the friction that often comes with authenticator apps or SMS codes. It hits the sweet spot between robust protection and a smooth user experience.
Seamlessly Integrating Voice into Multi-Factor Authentication
Security experts are unanimous: Multi-Factor Authentication (MFA) is a must. The problem is, traditional MFA can be a real headache for users, forcing them to juggle authenticator apps, text codes, or hardware keys. This friction often leads people to resist adopting it.
Voice biometrics offers a much smoother path forward. It can be easily slotted in as a powerful—and painless—second or third factor in any MFA setup.
- Effortless Verification: Instead of typing a code, a user just has to speak a simple passphrase.
- Reduced Friction: This makes security feel more like a natural conversation and less like a chore.
- Enhanced Security: It adds a robust biometric layer that is far tougher to crack than a one-time code sent via text, which can be intercepted.
Imagine logging into your banking app. You enter your password (factor one), and the app prompts you to say, "Show me my recent transactions." The system instantly verifies your voiceprint (factor two) and lets you in. It’s faster, easier, and worlds more secure than waiting for a text message. By adding voice to the mix, companies can seriously upgrade their security without frustrating their users.
For a deeper dive into how this technology is being applied today, check out our comprehensive guide on biometric voice authentication.
Seeing Voice Biometrics in Action Across Industries
The theory behind voice biometrics is one thing, but seeing it solve real problems is where it all clicks. This isn't some far-off, futuristic idea; it's a technology that's already changing how entire industries work, making things more secure and less frustrating for customers at the same time.
Let's move past the abstract benefits and look at the real-world impact. From locking down financial accounts to protecting patient privacy, voice biometrics replaces those clunky, annoying security hurdles with a simple, conversational checkpoint.
Revolutionizing Banking and Financial Services
The financial world is a massive target for fraud, so security has to be ironclad. The challenge? It also needs to be easy for legitimate customers to use. Voice biometrics is stepping in as the perfect middle ground.
- The Problem: Call center fraud is out of control. Scammers use stolen personal details to impersonate customers and take over accounts, because old-school security questions like "What was your first pet's name?" are ridiculously easy to bypass.
- The Solution: Banks are now using text-independent voice biometric authentication. As you speak naturally to a call center agent, the system works silently in the background, analyzing your voice and matching it to your unique voiceprint in just a few seconds.
- The Benefits: This passive check dramatically cuts down call times by getting rid of the security quiz. Even better, it acts as a powerful shield against account takeovers, which directly reduces fraud losses.
A major UK bank reported a 59% drop in phone fraud after bringing in voice biometrics. The system successfully authenticated over 17 million customer calls, proving it's not only effective but can handle massive scale in a high-stakes environment.
It’s also making mobile banking safer. Instead of fumbling with a long password, you can just say a simple passphrase into your phone to approve a big transaction. It’s a strong, simple layer of security that stops unauthorized transfers in their tracks.
Enhancing Security and Access in Healthcare
In healthcare, protecting patient data isn’t just good practice—it’s the law. Voice biometrics offers a secure and incredibly efficient way to control access to electronic health records (EHR) and other confidential information.
- The Problem: Doctors and nurses need to get into patient records quickly, often while they're on the move or have their hands full. Typing passwords into shared computers is slow and a major security weak point.
- The Solution: Hospitals are integrating voice authentication so medical staff can log into EHR systems with a quick voice command. This is a game-changer for telehealth, where a patient's identity has to be confirmed from afar before a virtual visit can begin.
- The Benefits: This hands-free login saves precious minutes, letting providers spend more time on what actually matters: patient care. It also creates a solid, auditable log of who accessed what records and when, making it much easier to stay compliant with privacy laws like HIPAA. You can learn more about how voice recognition software for medical professionals is transforming daily workflows.
Streamlining the Customer Experience in Call Centers
Beyond just banking, call centers in every industry are feeling the pressure to be faster, more helpful, and more secure. Voice biometrics helps them hit all three targets.
- The Problem: Nobody likes being grilled with security questions. It kicks off the call on a negative, untrusting note and wastes time for both the customer and the agent.
- The Solution: By authenticating callers passively within the first 15-20 seconds of a normal conversation, call centers can get rid of those knowledge-based questions for good.
- The Benefits: The result is a radically better customer experience. Agents are also freed up to focus on actually solving the customer's problem, which improves job satisfaction and makes the whole operation run smoother. It's no surprise the market for this technology is growing fast, with North America leading the charge thanks to its wide use in phone banking and customer service. As more companies realize that better security can also mean a better experience, this trend is only going to accelerate. You can dig into the numbers behind the global adoption of voice biometrics and its market growth.
Navigating Privacy and Compliance with Confidence

Whenever you introduce a new way for people to prove who they are, questions about privacy and data security are going to come up. It's only natural. With voice biometrics, you're asking users to trust you with something incredibly personal—their voice. Earning and keeping that trust means being crystal clear about how you handle their data and sticking to the rules.
The good news is that modern voice biometric systems are built from the ground up with privacy in mind. One of the biggest fears people have is that companies are keeping huge databases of recorded conversations, but that’s just not how it works. The system doesn't save the actual recording of your voice.
Instead, it creates a voiceprint. Think of this as a secure, encrypted mathematical map of your unique vocal patterns. It’s an abstract file that can't be reverse-engineered to reconstruct your voice, making it completely useless to a hacker if they ever got their hands on it. This simple fact is the cornerstone of user privacy in voice authentication.
Meeting Global Compliance Standards
Once you start collecting biometric data, you're playing in a different league when it comes to data privacy regulations. Laws like the General Data Protection Regulation (GDPR) in Europe have set a very high bar for how personal information, voiceprints included, must be handled. Getting it wrong can lead to massive fines and, just as bad, a serious blow to your reputation.
Here are the core principles you absolutely have to get right:
- Explicit Consent: Users must give you a clear "yes" to create and store their voiceprint. You need to tell them exactly what you’re collecting and why.
- Data Minimization: Only capture what you truly need for authentication. Nothing more.
- Purpose Limitation: That voiceprint should be used for one thing and one thing only: verifying the user's identity. Using it for anything else requires getting their permission all over again.
- Right to Erasure: People need a simple, no-fuss way to tell you to delete their voiceprint data for good.
To make sure you're covering all your bases, it’s wise to work through a detailed GDPR compliance checklist. Following these rules isn't just about avoiding legal trouble; it’s about showing your users you respect them.
Best Practices for Responsible Implementation
Beyond just ticking legal boxes, putting voice biometric authentication into practice responsibly is all about being proactive with security and transparency. The goal is to make every user feel secure and in control right from the start.
Building trust isn't a one-time action; it’s an ongoing commitment. A transparent privacy policy, coupled with strong technical safeguards, demonstrates that you value your users' security as much as they do.
Begin with a privacy policy that’s actually readable. Ditch the dense legal-speak and explain in plain language what a voiceprint is, how it's protected, and how a user can manage their own data. Top-notch encryption for voiceprints—both when they’re being sent and when they’re stored—is absolutely non-negotiable.
For a closer look at safeguarding this kind of sensitive information, it's worth exploring proven data security best practices. By making privacy a core part of your system's design from day one, you can offer an authentication experience that’s not just secure and convenient, but also worthy of your users' trust.
Integrating Voice Authentication into Your Ecosystem
Bringing voice biometrics into your company might sound like a massive technical lift, but it’s much more approachable when you break it down. The real goal is to find a solution that not only beefs up your security but also slots neatly into the systems you already rely on—whether that's a mobile app, a busy call center, or your internal network.
First things first: what are you actually trying to solve? Are you looking to slash call handle times in your IVR? Or maybe you need to lock down mobile banking transactions or give employees a way to log in without a password. Nailing down a clear objective from the start will shape your entire strategy and point you toward the right technology partner.
Choosing the Right Voice Biometric Partner
Picking a provider isn't just about the tech; it's about finding a long-term partner. You’ll want to look for a company that offers well-documented APIs and SDKs (Software Development Kits) that your developers can actually work with. Good documentation and responsive support can make the difference between a smooth integration and a painful one.
Beyond the technical checklist, here’s what you should really be looking for:
- Scalability: Will this system keep up as you grow? You need something that can handle your busiest days without breaking a sweat.
- Security and Compliance: Does the provider meet global standards like GDPR and SOC 2? Their dedication to data protection is non-negotiable and fundamental to earning your users' trust.
- Accuracy and Liveness Detection: The core technology has to be incredibly accurate. It needs to correctly identify legitimate users while also being smart enough to shut down spoofing attempts from recordings or deepfakes.
A successful integration really comes down to finding a partner whose technology fits your long-term vision. The best solutions are built to be flexible, giving you room to adapt as your security needs change over time.
Best Practices for a Seamless User Rollout
Once the tech is in place, the focus has to shift to your users. A security system is useless if no one wants to use it. Today, the push for voice biometrics is often driven by the new realities of remote work, where verifying someone's identity from afar is essential. The technology uses a person's unique vocal patterns—things like pitch, tone, and speech rhythm—to confirm it's really them, protecting sensitive company data. People are also just getting more comfortable talking to devices, thanks to the AI in smart home assistants. You can find more on the key drivers of the voice biometrics market and its projected growth.
To get people on board, start by being transparent. Explain the benefits to your customers or employees, highlighting both the stronger security and the simple convenience of ditching passwords. The enrollment process has to be dead simple; if it's clunky or confusing, you’ll lose them.
Think about rolling it out in phases. Start with a smaller pilot group to work out the kinks and gather feedback before going live for everyone. In fields like law, where client confidentiality is everything, hesitating to adopt stronger security measures is a huge liability. You can read more about the biggest risk of waiting to adopt AI for lawyers.
By turning the abstract idea of "integration" into a concrete, user-focused plan, you can build a system that’s both more secure and genuinely easier to use.
Got Questions? Here Are Some Straight Answers
Even when you get the concept, real-world questions always pop up. As voice biometrics become more a part of our daily lives, it’s only natural to wonder about the specifics. What happens if I get a cold? How safe is my data, really?
Let's walk through the most common questions people ask. We'll clear up any confusion and give you the confidence that this technology is built for real life.
Can Someone Use a Recording of My Voice to Break In?
This is the big one, and it's a valid concern. Early versions of this technology could be tricked, but that’s ancient history now. Modern systems use something called "liveness detection," and it’s a game-changer.
Think of it as a built-in reality check. The system analyzes tiny, almost imperceptible acoustic details and frequency shifts that only happen when a person is speaking live. Recordings and deepfakes just don't have these natural micro-variations. So, the system isn't just asking who is speaking—it's confirming they're a live person speaking right now. It's a simple but incredibly effective way to shut down impersonation attempts.
What Happens If My Voice Changes?
We all have off days. Maybe you have a cold, you're standing in a noisy train station, or you're just plain exhausted. Voice biometric systems are designed with this in mind.
Your voiceprint isn’t just one thing; it’s a complex model based on over 100 different physical and behavioral vocal characteristics. A sore throat might temporarily affect a few of them, but the vast majority of your core identifiers stay the same.
The system is smart enough to focus on the permanent, underlying structure of your vocal tract—the parts that a head cold can't touch. While a really bad case of laryngitis might be an issue, everyday things like a slight illness, background chatter, or a change in your mood won't stop you from getting authenticated. The system is built to be resilient.
Is a Recording of My Voice Stored Somewhere?
No, and this is a crucial point for privacy. The system never keeps an audio file of your voice. When you enroll, your speech is analyzed and immediately converted into a secure, encrypted mathematical model. We call this a voiceprint.
Here’s why that matters:
- It’s an abstract formula: Your voiceprint is a string of numbers that represents your unique vocal patterns. It's not an audio file you can play back.
- It’s a one-way street: The voiceprint can't be reverse-engineered to reconstruct your actual voice. To a hacker, the data is meaningless.
- Your privacy is protected: Since only the mathematical data is stored, the words you say remain completely private.
This method keeps your biometric data fundamentally secure. It’s the same core principle that allows businesses to use voice to text AI for improving workflows without compromising security. Your voice creates the key, but the key itself isn't a recording.
Ready to transform your document workflow with secure, efficient dictation? Whisperit uses powerful AI to help you create and edit documents up to two times faster, all while protecting your data with Swiss-hosted encryption and full compliance. Discover how Whisperit can streamline your work today.