A Guide to Data Privacy Impact Assessment
Think of a Data Privacy Impact Assessment (DPIA) as a vital health check for any project that handles personal data. It’s a structured process you use to get ahead of potential privacy problems, identifying and minimizing risks before they can harm individuals or tarnish your company's reputation.
It's less about ticking a compliance box and more about building a solid foundation of trust.
Your First Line of Defense in Data Privacy

A DPIA fundamentally shifts your approach from reactive damage control to proactive, strategic risk management. It forces you to pause and ask the tough questions right at the start.
Are we collecting more data than we absolutely need? How could this new system be exploited? What’s the real-world impact on the people whose data we’re processing? Answering these questions early on saves you from making costly and reputation-damaging mistakes later.
This proactive stance isn't just a good idea—it's increasingly the law. Regulations like the GDPR set a global standard, and it's estimated that by the end of 2024, 75% of the world's population will be covered by modern privacy laws. With over 160 such laws now in effect globally, you can't afford to be reactive.
When Is a DPIA Mandatory?
Knowing when to conduct a DPIA is half the battle. Some projects carry such a high potential risk to people's rights and freedoms that a formal assessment isn't just recommended; it's legally required. The table below breaks down some of the most common triggers that should immediately put a DPIA on your radar.
| Triggering Condition | Description | Real-World Example |
|---|---|---|
| Systematic and Extensive Evaluation | Using algorithms or automation for profiling or making decisions that significantly impact people's lives (e.g., job or credit applications). | An HR tech company developing an AI tool that automatically screens and ranks job candidates based on their online presence and submitted data. |
| Large-Scale Processing of Sensitive Data | Handling special categories of data like health information, biometrics, genetics, or criminal records for a large number of individuals. | A health tech startup launching a new wearable device and app that collects and analyzes users' biometric data, like heart rate and sleep patterns. |
| Systematic Monitoring of Public Areas | Using technology to observe, monitor, or track people in a publicly accessible space on a large scale. | A city council's plan to install a network of high-definition CCTV cameras with facial recognition capabilities in its downtown shopping district. |
| Innovative Use of New Technology | Implementing new or novel technologies (like advanced AI, IoT, or biometrics) where the privacy implications are not yet fully understood. | A retail company deploying smart shelves that use IoT sensors and facial analysis to track shopper behavior and demographics in real-time. |
Ultimately, if your gut tells you a project could deeply affect individuals' privacy, it’s always best to err on the side of caution and conduct a DPIA.
Real-World Scenarios That Demand a DPIA
Let's move from theory to practice. Here are a couple of concrete examples where a DPIA is an absolute must.
Imagine a large retail chain wants to launch an AI-powered analytics platform. The goal is to track customers' in-store movements via their phone's Wi-Fi signal, combine it with their online browsing history, and build detailed profiles for hyper-targeted ads. This project clearly involves profiling and novel technology, hitting multiple triggers for a mandatory DPIA.
Another classic case is a telehealth company developing a new app for remote patient monitoring. The app collects continuous health data—blood pressure, glucose levels, and even mental health survey responses. Because this involves the large-scale processing of sensitive health data, a DPIA is non-negotiable.
A well-executed DPIA isn’t just an expense; it’s an investment. It transforms data protection from a legal headache into a competitive advantage by building customer trust and steering clear of massive fines.
Conducting a DPIA is a cornerstone of strong data security compliance. It's the practical mechanism that proves your data handling practices are both legal and ethical.
Understanding these obligations is key to building a resilient, trustworthy organization. To learn more about navigating these requirements, you can explore our in-depth guide: https://www.whisperit.ai/blog/data-privacy-compliance
Building Your DPIA Team and Defining Scope

A Data Privacy Impact Assessment is not a one-person job. Trust me, I've seen organizations try to run them in a silo, and it almost always ends in missed risks and overlooked operational details. True success hinges on collaboration.
Think of it like putting together a crew for a complex mission. You need a mix of specialists—the navigator, the engineer, the strategist—to see the entire landscape. The same holds true for a DPIA. Your first move is to identify the key players who will bring their unique perspectives to the table.
Assembling Your Core Stakeholders
A rock-solid DPIA team is always cross-functional, drawing expertise from different corners of the business. While the job titles can change from company to company, these roles are almost always non-negotiable.
- Data Protection Officer (DPO) or Privacy Lead: This is your guide. They steer the entire process, making sure you’re ticking all the legal boxes and acting as the central hub for the assessment. Their grasp of privacy law is invaluable.
- Project Manager: This person knows the project’s goals, timelines, and technical guts better than anyone. They provide the essential context—the what and the why behind the initiative.
- IT Security and Engineering Leads: Your technical wizards. They can break down how data is actually stored, encrypted, moved, and secured. They’ll spot the vulnerabilities others won’t.
- Legal and Compliance Counsel: While the DPO is zeroed in on privacy law, your general counsel can flag broader contractual obligations, liabilities, and other regulatory red flags.
- Business or Product Owners: These are the people who own the "business case." They clarify why you're processing the data in the first place, ensuring the DPIA's findings align with the company's strategic objectives.
Getting these folks in the room from day one is critical. It helps you bake privacy into the project from the start, rather than trying to slap it on at the end like a coat of paint.
Defining a Clear and Focused Project Scope
With your team assembled, your next mission is to lock down the project scope. A fuzzy scope is the single biggest reason DPIAs fail. It leads to wasted hours, undiscovered risks, and a final report that’s too vague to be useful. You need to draw a sharp, clear line around what you are assessing.
Start by mapping out the entire data lifecycle. I mean every single touchpoint.
- Collection: How and from where is personal data coming in?
- Processing: What are you actually doing with it once you have it?
- Storage: Where does it live, and how is it secured?
- Sharing: Is it being sent to any third-party vendors or partners?
- Retention & Deletion: How long are you keeping it, and what's the plan for getting rid of it securely?
A DPIA's effectiveness is directly proportional to the clarity of its scope. A fuzzy scope guarantees a fuzzy assessment, leaving your organization exposed to hidden risks.
A stakeholder workshop is the best way to get everyone on the same page and prevent scope creep. This isn't just another meeting; it's a dedicated working session to map data flows, confirm the tech stack, and agree on the precise boundaries of the assessment.
To make sure you don't miss anything, it helps to follow a structured approach. Using a solid project scope template can provide the framework you need to document everything clearly. This document will become the bedrock of the entire DPIA process.
Pinpointing and Weighing Privacy Risks
With your team in place and the project's boundaries clearly mapped out, it's time to dive into the core of the DPIA. This is where you shift from planning to a deep-dive investigation, systematically uncovering every potential privacy risk your project might create. You need to wear two hats here: think like the people whose data you're processing, and also think like someone who might misuse it.
The objective is to identify any plausible threat to an individual's rights and freedoms. This isn't just about preventing a data breach; it's much broader. You have to consider the full spectrum of negative outcomes that could ripple out from your data processing activities.
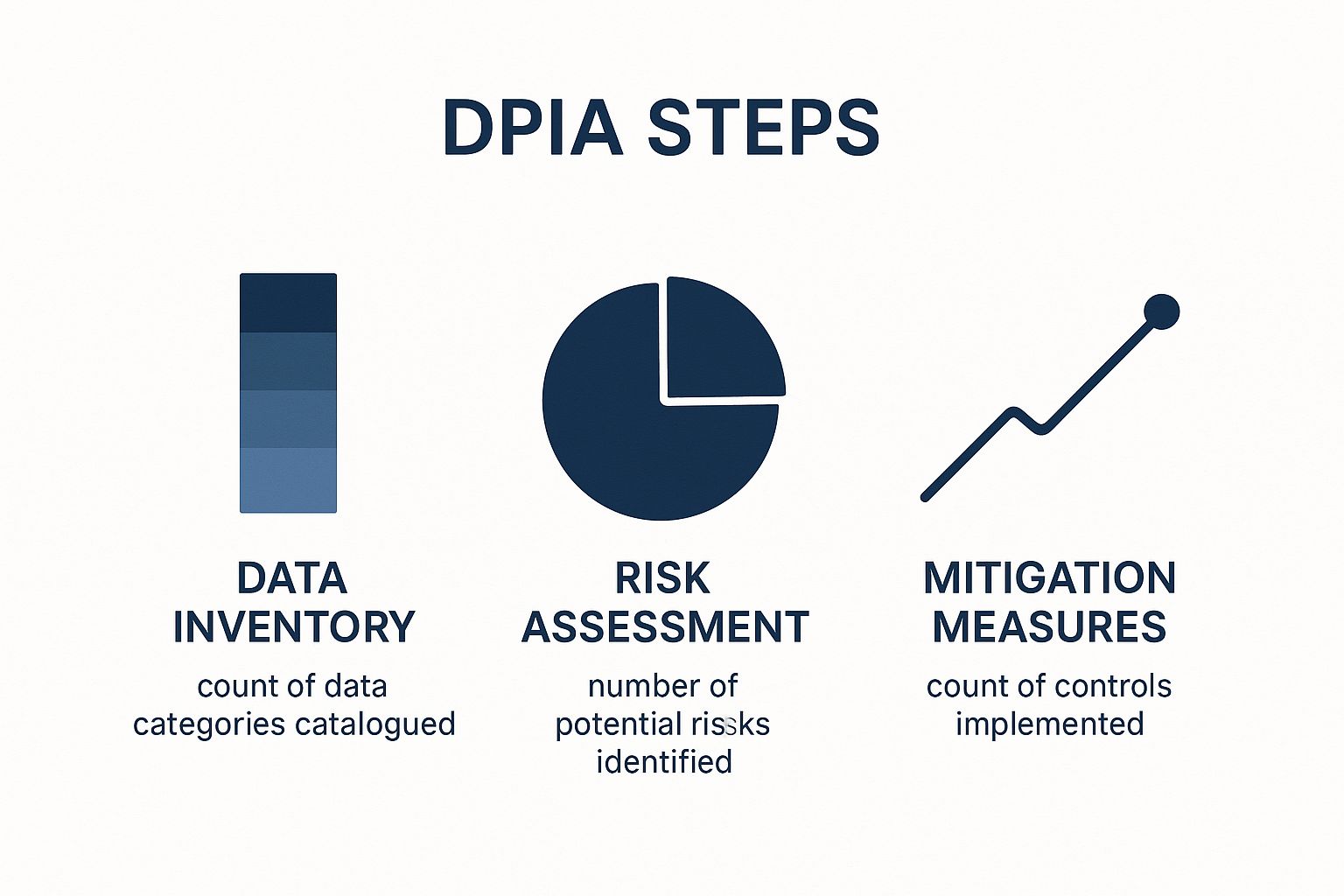
As you can see, a comprehensive data inventory almost always surfaces a number of risks. Each one of these will require a specific, targeted control to bring it back into an acceptable range.
Unearthing Potential Threats
Let's ground this in a real-world scenario. Imagine a company is rolling out a new HR analytics platform. It will pull in employee performance reviews, salary figures, attendance logs, and even peer feedback to spot promotion candidates and employees who might be at risk of leaving.
So, what could go wrong? The list is longer than you might think.
- Unauthorized Access: A manager peeks at salary data for employees outside their direct team, sparking internal conflict and trust issues.
- Function Creep: The platform was built for promotion analysis. A year later, it's quietly repurposed to make automated decisions about layoffs without a new assessment.
- Inaccurate Conclusions: A biased algorithm or bad data mistakenly flags a star performer as a "churn risk," unfairly damaging their career prospects.
- Algorithmic Discrimination: The system unintentionally learns and amplifies existing biases in historical data, putting certain demographic groups at a disadvantage for promotions.
- Re-identification Risk: Even if the data is "anonymized," someone could potentially link different datasets (like attendance and project assignments) to re-identify individuals and their sensitive performance details.
The most dangerous privacy risks aren't always the most obvious. Subtler threats like algorithmic bias or function creep can cause just as much harm to individuals as a straightforward data leak.
This brainstorming phase is absolutely critical. Get your cross-functional team in a room and encourage them to think creatively about what could realistically go wrong from every angle—technical, procedural, and human.
How to Evaluate Risk Likelihood and Impact
Once you have a running list of potential privacy risks, you need to prioritize. Not all risks are created equal. The probability of a sophisticated state-sponsored attack on your HR platform is probably a lot lower than a well-meaning manager simply misinterpreting an analytics report.
A simple but incredibly effective tool here is a risk matrix. You'll score each risk you've identified on two dimensions:
- Likelihood: How likely is this to actually happen?
- Impact: If it does happen, how severe is the harm to the people affected?
By assigning a simple score (say, 1-5 for both likelihood and impact), you can quickly see which issues demand your immediate attention. Anything with a high likelihood and a high impact score shoots straight to the top of your to-do list. This structured approach is fundamental to any good risk management framework. For a closer look at the mechanics, our guide on how to conduct a risk assessment is a great resource.
This isn't just a best practice; it's fast becoming the standard. A recent study found that 39% of organizations now report conducting DPIAs as a key performance metric. This surge is a direct response to escalating digital threats and regulatory heat, with massive fines against companies like Meta (over $1 billion**) and TikTok (**$360 million) serving as cautionary tales.
Let's take a look at some common risks that come up during DPIAs and how they can be managed.
Common Privacy Risks and Mitigation Measures
This table offers a snapshot of frequent privacy risks and the types of controls—both technical and organizational—that can effectively address them.
| Privacy Risk | Potential Impact on Individuals | Example Mitigation Measure |
|---|---|---|
| Excessive Data Collection | Increased exposure in a breach; feeling of surveillance; potential for misuse. | Implement data minimization principles; only collect fields absolutely necessary for the stated purpose. |
| Lack of Transparency | Individuals feel powerless and unaware of how their data is used, eroding trust. | Provide clear, layered privacy notices at the point of data collection; maintain an updated public privacy policy. |
| Secondary Use (Function Creep) | Data is used for a new purpose without consent, potentially leading to unfair or unexpected outcomes. | Enforce purpose limitation controls; require a new DPIA and legal review before data is used for a new purpose. |
| Algorithmic Bias | Automated decisions unfairly disadvantage individuals based on protected characteristics. | Regularly audit algorithms for bias; use diverse and representative training data; provide a human review process for high-stakes decisions. |
| Inadequate Security | Data breach leads to identity theft, financial loss, or reputational damage. | Implement encryption (at rest and in transit); enforce strong access controls and multi-factor authentication. |
Thinking through these common scenarios can help jump-start your own risk identification process, ensuring you cover the most critical bases.
By systematically identifying and then scoring these risks, you turn a vague sense of unease into a structured, actionable plan. This sets you up perfectly for the next step: figuring out how to fix it all.
Adapting Your DPIA for AI and New Tech
The classic data privacy impact assessment is a great starting point, but it wasn't built for the wild world of artificial intelligence. Traditional DPIAs are designed for predictable, rules-based systems. AI, on the other hand, is a whole different beast—it's dynamic, constantly learning, and often operates like a "black box," making it incredibly difficult to pin down the privacy risks.
Let's be blunt: you can't evaluate a sophisticated machine learning model with the same checklist you'd use for a simple customer database. The game has changed. We're not just worried about a data breach anymore; we're now grappling with algorithmic bias, automated decisions that can affect millions, and a troubling lack of transparency.
Beyond Standard Risk Categories
When you’re kicking off a DPIA for an AI system, you have to think bigger. Sure, the usual risks like unauthorized access still matter, but AI introduces some new and frankly, more sinister, threats. Your assessment needs to dig into these head-on.
- Algorithmic Bias: Is your training data a reflection of past prejudices? If so, your AI will learn and amplify them. Think of an AI hiring tool trained on a company's historical hiring data—it might start unfairly rejecting qualified candidates simply because they don't fit a biased historical pattern.
- The 'Black Box' Problem: Can you actually explain why the AI made a certain decision? If your model denies someone a loan, you'd better be able to explain the reasoning. Opaque, unexplainable decisions are a massive liability for your company and can be devastating for the individual.
- Large-Scale Profiling: AI is scarily good at connecting the dots. It can sift through massive datasets to build incredibly detailed profiles, often guessing sensitive things about people that they never shared. This opens a Pandora's box for potential misuse and manipulation.
Imagine a city rolling out an AI-powered traffic management system. A standard DPIA would probably focus on encrypting the sensor data. But an AI-savvy DPIA would ask the tough questions: Could this system be used to track where people go every day? Could it infer their personal routines? Could it build detailed citizen profiles without anyone ever knowing?
Asking the Right Questions About AI
To get a real handle on these new risks, your DPIA questionnaire needs a serious update. This isn't just a job for the privacy team anymore. You need to pull in your data scientists and AI ethicists—the people who live and breathe this stuff—to help translate the tech into tangible privacy risks.
Your updated assessment should be asking questions like these:
- Training Data Integrity: Where did the training data come from? Was it sourced ethically and with real consent? What have you done to find and root out any biases?
- Model Validation: How was the model tested? Did you check for accuracy, fairness, and performance across different groups of people? What are its known blind spots and error rates?
- Explainability and Transparency: If the AI's decision impacts someone, can you give them a clear, simple explanation of how it happened?
- Human Oversight: Is there a human in the loop? There needs to be a clear process for someone to step in, review, and override the AI, especially when the stakes are high. Who’s ultimately accountable when the model messes up?
The sheer growth of AI is forcing a reckoning in the privacy world, and both the public and regulators are getting nervous. In 2024 alone, AI-related incidents shot up by 56.4%. It's no surprise that public trust is tanking—only 47% of people believe AI companies will actually protect their data. This has spurred 80.4% of U.S. local policymakers to demand tougher rules.
For AI, a DPIA is no longer a simple box-ticking exercise. It's become a crucial instrument for ethical governance, forcing you to think about the real-world, societal impact of your tech before you launch it.
Getting ahead of this is just smart business, especially as new laws are being written to tackle these exact issues. You need to be aware of emerging regulations like the California AI law, which is already setting new benchmarks for transparency and accountability. A modern, AI-aware DPIA doesn't just keep you compliant today; it builds a more resilient and trustworthy organization for whatever comes next.
Turning Your DPIA Findings Into Action

Let’s be honest: a data privacy impact assessment that ends up collecting dust on a digital shelf is worthless. The real work begins after you’ve identified the risks. This is where you roll up your sleeves and turn those findings into a concrete remediation plan, moving your project from analysis to action.
The objective isn’t to chase the fantasy of zero risk—that’s just not practical. The goal is to bring risks down to a manageable, acceptable level. This usually involves a smart combination of technical safeguards, updated policies, and smarter procedures.
Developing and Prioritizing Your Fixes
Once you've scored each risk based on its likelihood and potential impact, you'll naturally see which fires need to be put out first. The high-risk items jump to the top of the list, while the lower-level concerns can be scheduled for later.
Your solutions will likely fall into three main buckets:
- Technical Controls: These are the safeguards baked directly into your technology. Think implementing end-to-end encryption for data transfers, enforcing multi-factor authentication, or using pseudonymization to de-identify personal data.
- Organizational Policies: These are the formal rules that guide how your team handles data. You might need to tighten up your data minimization policy to stop over-collection, make your consent forms more transparent, or finally create that strict data retention schedule you’ve been talking about.
- Procedural Changes: This is all about tweaking daily workflows. For example, you could add a mandatory human review step before an automated system makes a high-stakes decision or build a more efficient process for handling data subject access requests.
For every risk you found, document the specific fix. If you flagged a risk of "function creep" with a new HR analytics tool, your mitigation measure would be a new policy: the tool can't be used for any other purpose without a new DPIA and explicit approval.
Your remediation plan is your roadmap from identifying a problem to solving it. It’s the tangible proof that you’ve not only spotted potential harm but have taken solid steps to prevent it. This is what shows regulators you're serious and builds real trust with your users.
Assigning Owners and Deadlines
A plan without names and dates attached is just a wish list. Every single mitigation task needs a champion—a specific person or team responsible for getting it done. Vague assignments like "the IT team" just don't work.
Get specific. Who is actually implementing the new encryption standard? Who is rewriting the privacy notice? Who is training the support team on the new data access workflow?
Next to each owner, add a realistic deadline. This creates accountability and keeps the momentum going. A well-structured plan, which you can build using insights from a strong compliance audit checklist, turns abstract risks into a clear set of tasks with firm completion dates.
Putting Together the Final DPIA Report
Think of the final DPIA report as more than just a box-ticking exercise. It's the official record of your entire privacy journey for this project. It’s the document you’d confidently hand over to an auditor, a regulator, or your own board to prove you did your due diligence.
The report needs to be clear, concise, and complete. It should summarize the essentials:
- Project Description: What is this project and what is it trying to achieve?
- Data Flows: A clear map showing how personal data moves through the system.
- Consultation: A record of who you talked to during the process (stakeholders, data subjects, etc.).
- Identified Risks: A detailed breakdown of the privacy risks you uncovered.
- Mitigation Measures: The specific actions you've committed to taking for each risk.
- Residual Risk: Your assessment of the risk that remains after your fixes are in place.
- Sign-Off: The official green light from the project owner and your Data Protection Officer (DPO).
This document becomes your proof of responsible data stewardship. It demonstrates that you’ve thought through the privacy implications and have a solid plan to protect the people whose data you’re handling.
Lingering Questions About Data Privacy Impact Assessments
Even the most seasoned teams run into questions when working through a Data Privacy Impact Assessment. It's the nature of the beast—blending technology, legal obligations, and the very real rights of individuals. Let's tackle some of the most common questions that come up.
How Often Is a DPIA Really Needed?
Think of a DPIA not as a one-time checkbox, but as a living document tied to your project's lifecycle. You absolutely must complete one before you kick off any new project that's likely to result in a high risk to personal data.
But it doesn't stop there. If the project changes in a meaningful way—the scope expands, you bring in a new vendor, or you start processing data for a completely new reason—it's time to revisit and update your DPIA. As a rule of thumb, it's smart to formally review it at least every three years, even if nothing major seems to have changed.
Isn't This Just Another Risk Assessment?
Not quite. While they share a similar name, a general risk assessment and a DPIA look at risk from two completely different angles.
A typical cybersecurity or business risk assessment focuses on threats to the organization. We're talking about financial loss, system downtime, or a hit to your reputation.
A DPIA, on the other hand, flips the script. It is laser-focused on the risks to the rights and freedoms of the individuals whose data you're handling. This means evaluating the potential for things like discrimination, identity theft, or a breach of confidentiality.
The crucial mindset shift is from "What's the risk to our business?" to "What's the risk to the people this data belongs to?"
Do We Have to Make Our DPIA Public?
There's generally no legal mandate under regulations like GDPR to publish your full DPIA for the world to see. That said, transparency is a huge part of modern data protection.
Many organizations choose to publish a high-level summary. It’s a great way to build trust with your users and show you're serious about protecting their information. You are, however, obligated to share the full report with your supervisory authority if they ask for it. This is especially true if you’ve flagged high risks that you can't completely eliminate.
For a deeper dive into these kinds of details, this comprehensive guide to mastering the Data Protection Impact Assessment is an excellent resource.
What Happens if We Find a High Risk We Can't Fix?
This is the big one. If your DPIA uncovers a high risk to people's rights that you simply can't mitigate with your planned safeguards, you can't just move forward.
The law is clear: you are required to consult with your data protection supervisory authority before starting any processing.
They will review your DPIA and provide official advice. They might give you the green light, suggest additional measures, or, in some cases, prohibit the processing altogether. Skipping this step is a major compliance violation and can lead to hefty fines. It’s a critical stopgap to ensure you’re not taking unnecessary risks with people’s data.
At Whisperit, we understand that handling sensitive information requires tools built with privacy at their core. Our AI-powered dictation and editing platform is designed to help professionals in legal, healthcare, and other sectors create documents faster without compromising on security. Hosted in Switzerland and fully compliant with GDPR and SOC 2, Whisperit ensures your data remains protected, allowing you to focus on what you do best. Streamline your workflow securely at https://whisperit.ai.